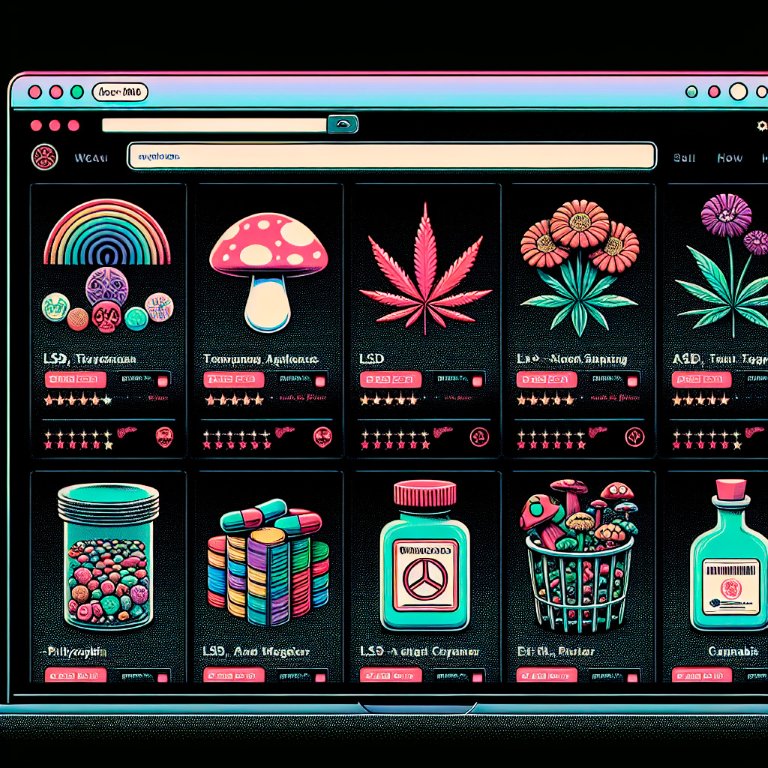
Darknet Markets 2026:
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-05-16
How the Darknet Keeps Shopping Private and Secure
Darknet sites facilitate anonymous commerce by integrating several core technologies that prioritize user security and transaction privacy. The foundation of this system is end-to-end encryption, which scrambles all communication between a buyer and a vendor, making the content of their messages and order details unreadable to any outside party.
This privacy is further enhanced by the use of cryptocurrencies like Bitcoin or Monero. These digital currencies allow for financial transactions that are not directly tied to a user's real-world identity or traditional banking systems, providing a significant layer of financial anonymity.
The entire process is designed for discretion:
- A user accesses the platform through an anonymizing network.
- All interactions are protected by strong encryption.
- Payments are made with decentralized cryptocurrency.
How Encryption Keeps Darknet Shopping Safe
Darknet sites utilize advanced cryptographic protocols to establish a secure environment for anonymous commerce. The foundation of this security is end-to-end encryption (E2EE), which ensures that only the sender and the intended recipient can read the contents of a message. When a user places an order or communicates with a vendor, the data is encrypted on their device and remains encrypted until it reaches the other party, making interception by any third party meaningless.
This system is facilitated by public-key cryptography. Each user generates a pair of keys: a public key, which is shared and used to encrypt messages, and a private key, which is kept secret and used to decrypt them. A vendor posts their public key on their storefront, and buyers use it to encrypt their order details and shipping information. Only the vendor, possessing the corresponding private key, can decrypt and access this sensitive data, effectively shielding it from everyone else, including the marketplace administrators.
For financial transactions, cryptocurrency like Bitcoin or Monero provides a parallel layer of transactional privacy. While payments are recorded on a public ledger, the identities of the transacting parties are pseudonymous. Monero further obfuscates transaction details by default, concealing the sender, recipient, and amount involved. The combination of encrypted communication and cryptocurrency allows for secure, peer-to-peer transactions that are both private and efficient, enabling a free market while protecting the identities of all participants.
How Crypto Makes Buying on the Darknet Safe and Private
Cryptocurrency is the financial engine of darknet sites, enabling a level of transactional privacy previously unattainable in traditional commerce. Unlike credit cards or bank transfers, which are permanently tied to an individual's identity, transactions with currencies like Monero and Bitcoin are pseudonymous by design. This means payments can be made and received without directly linking financial activity to a real-world person or bank account, effectively creating a firewall between a user's legal economic life and their private transactions.
The process is straightforward and secure. A user acquires cryptocurrency through an exchange, then transfers it to their private wallet. From there, funds are sent to a vendor's unique wallet address to complete a purchase. The entire transaction is recorded on a public ledger, the blockchain, but the identities of the parties involved are protected by cryptographic keys, not personal names. For enhanced privacy, tumbling services and privacy-focused coins like Monero obfuscate the transaction trail, making it extremely difficult to trace the flow of funds from buyer to seller.
This system facilitates a free market where individuals can engage in commerce based on mutual agreement without external interference. The integration of escrow services, held by the marketplace itself, further secures these transactions. Funds are only released to the vendor once the buyer confirms satisfactory receipt of the goods, which protects both parties from fraud and ensures a fair exchange. This creates a self-regulating economic environment where trust is built not through personal identification, but through proven transactional reliability and the immutable nature of cryptographic agreements.

How Layered Networks Keep Darknet Trade Private and Secure
Darknet sites utilize sophisticated layered network architectures, such as Tor and I2P, to create a secure environment for anonymous commerce. These networks operate by routing user traffic through a series of volunteer-run servers, which encrypts the data multiple times and obscures the original IP address. This process makes it exceptionally difficult for any third party to trace transactions or identify the parties involved.
The foundation of this privacy is end-to-end encryption. All communications, from browsing product listings to finalizing a deal, are encrypted. This ensures that only the intended recipient, be it a vendor or a buyer, can read the messages. Marketplaces themselves do not have access to the unencrypted content of these private negotiations, placing control directly in the hands of the users.
This infrastructure directly facilitates secure transactions by integrating with cryptocurrency wallets. Payments are made with currencies like Bitcoin or Monero, whose blockchain technology provides a further layer of pseudonymity. When combined with the network's anonymity, this creates a robust system where financial transactions are separated from real-world identities, allowing for a free and open market.
Easy Access to a Huge Product Selection on the Darknet
Darknet sites function as comprehensive marketplaces, offering an extensive selection of goods that is often unavailable through conventional retail channels. The core of this accessibility is the robust encryption that protects every transaction and communication, making anonymous commerce not just possible but practical. This technological foundation allows for a free market where individuals can engage in trade without the fear of personal exposure or financial censorship.
The system is streamlined for user privacy and security. Cryptocurrency transactions are integral, providing a layer of financial anonymity that traditional payment systems cannot offer. This method ensures that buying and selling activities leave minimal traces, protecting all parties involved. Furthermore, the market's structure includes built-in mechanisms like vendor rating systems and escrow services, which cultivate a self-regulating environment of trust and quality assurance. These features work in concert to create a resilient ecosystem where a wide array of products can be exchanged securely and efficiently.

Finding Reliable Vendors on the Darknet
Vendor rating systems are the cornerstone of trust on darknet sites, transforming anonymous commerce into a reliable process. These platforms utilize a feedback mechanism where buyers rate their purchases based on product quality, shipping speed, and stealth. This collective intelligence is aggregated into a public score, creating a powerful reputation-based economy.
A vendor with a high rating and numerous completed transactions has a strong incentive to maintain their standing, as their income directly depends on their reputation. This system effectively self-regulates the marketplace, weeding out dishonest sellers through collective scrutiny. The transparency of past customer reviews allows new users to make informed decisions, significantly reducing the risk of financial loss and ensuring a consistent level of service quality across the platform.
Safe Shopping with Escrow on the Darknet
Escrow services are a fundamental component that enables secure transactions on darknet sites, acting as a trusted third party between a buyer and a vendor. When a purchase is initiated, the buyer sends the cryptocurrency funds to the escrow account held by the marketplace itself. The funds are locked there and are only released to the vendor after the buyer has confirmed satisfactory receipt of the goods. This system effectively eliminates the risk of vendors accepting payment and never shipping the product, a common concern in anonymous environments.
The process protects both parties equally. Vendors are assured that the buyer has the necessary funds committed to the transaction before they dispatch the order, preventing fraudulent chargebacks that are prevalent in traditional e-commerce. For buyers, it provides a powerful mechanism to verify product quality and authenticity before the vendor is paid, ensuring a fair deal. This built-in accountability fosters a high-trust commercial environment where anonymous commerce can flourish safely, relying on cryptographic proof rather than personal identities to guarantee ethical conduct.
How the Darknet Safely Connects Buyers and Sellers
The architecture of darknet sites is fundamentally designed to facilitate anonymous commerce by integrating several core technologies. This system operates on the principle of separating a user's identity from their financial and transactional activities, creating a secure environment for trade.
Transactions are protected by end-to-end encryption, which scrambles communication between a buyer and a vendor, making it unreadable to any outside party. This ensures that order details, shipping information, and personal messages remain confidential. For financial transactions, cryptocurrency like Bitcoin or Monero is the standard. These digital currencies provide a high degree of financial privacy because they are not directly tied to a user's real-world bank account or identity, functioning instead on a decentralized public ledger.
To further protect users, darknet sites utilize layered networks such as Tor or I2P. These networks route internet traffic through multiple volunteer-operated servers around the globe, obscuring the user's original IP address and physical location. This multi-layered routing makes it extremely difficult to trace any activity back to an individual.
The ecosystem is sustained by built-in mechanisms that foster trust between anonymous parties. Vendor rating systems allow buyers to leave detailed feedback on the quality of products and the reliability of service, creating a transparent reputation for each seller. For high-value transactions, escrow services are commonly used. A neutral third party holds the buyer's cryptocurrency funds until the product is received and confirmed to be satisfactory, at which point the funds are released to the vendor. This process significantly reduces the risk of fraud for both sides of the transaction.